As a manufacturer at Genuine Printing, we deeply understand the unique challenges you face as a bulk purchaser in today’s increasingly complex global market. Counterfeiting and fraudulent activities are rampant, posing severe threats to corporate reputation, financial health, and supply chain integrity. We are committed to providing you with the most advanced security paper solutions to effectively combat these risks.
This article will delve into the core technologies of security paper and, from a manufacturer’s perspective, reveal how to evaluate the true cost-effectiveness of these cutting-edge anti-counterfeiting features. Our goal is to ensure your procurement decisions not only deliver immediate security but also achieve long-term strategic value and significant return on investment.
The Imperative of Security Paper in Modern Procurement
The Grave Challenge of Counterfeiting and Fraud: Unignorable Economic Losses
The global economy is suffering immense impacts from counterfeit and pirated goods. In 2018, worldwide counterfeiting was estimated to cost the global economy between USD 1.7 trillion and USD 4.5 trillion annually, also resulting in over 70 deaths and 350,000 serious injuries each year. The International Chamber of Commerce predicts that sales of counterfeit items could reach USD 4.2 trillion by the end of 2025. These alarming figures not only signify direct financial losses but also highlight profound impacts on brand reputation, consumer trust, and public safety, underscoring the necessity of robust anti-counterfeiting measures.
These statistics are more than just cold numbers; they reveal a stark reality: the harm caused by counterfeit products extends far beyond economic considerations. The annual cases of deaths and serious injuries due to counterfeiting elevate anti-counterfeiting efforts from a mere business concern to a matter of public safety and corporate social responsibility. For bulk purchasers, especially in industries with extremely high product safety requirements, such as pharmaceuticals, food, or critical components, this means that investing in security paper is no longer just about protecting their own financial bottom line, but also about fulfilling their commitment to consumer health and market integrity. This dedication to ethics and social responsibility can significantly enhance a company’s long-term brand value and market reputation.
Strategic Considerations for Bulk Purchasers: Beyond Initial Costs
As a bulk purchaser, you understand that procurement decisions extend far beyond the initial purchase price. Counterfeit products can trigger a domino effect on your operations: from revenue loss and market share erosion to legal lawsuits, regulatory fines, and ultimately, a decline in customer trust and damage to brand value. For instance, a Pew Research Center survey found that 72% of consumers consider the presence of counterfeit products a major problem, and 61% are less likely to trust brands frequently associated with counterfeits. Therefore, investment in security paper should be viewed as a strategic move aimed at reducing Total Cost of Ownership (TCO) and achieving a substantial Return on Investment (ROI).
These statistics clearly indicate that consumer concern over counterfeit products is growing, directly impacting their trust in brands. This implies that if your products or documents are easily counterfeited, consumers might develop doubts about your brand, even if you offer excellent products or services. This erosion of trust can lead to customer churn, decreased market share, and long-term depreciation of brand assets. Therefore, we believe that investing in security paper is not merely a defensive expenditure, but an active mechanism for brand protection and customer loyalty. By incorporating clearly identifiable anti-counterfeiting features into documents and products, you send a clear signal to the market: you are committed to providing authentic, reliable products, thereby reinforcing consumer confidence, promoting repeat purchases, and ultimately protecting and enhancing your brand value.
Security Paper Technology Explained: Deconstructing Cutting-Edge Anti-Counterfeiting Features
Security paper is a specialized paper that incorporates features to identify or authenticate a document as original, and to demonstrate tamper evidence when fraud is attempted. These features are typically categorized into three levels: overt, covert, and forensic. This layered design offers bulk purchasers flexible and targeted security solutions. By classifying anti-counterfeiting features into these three clear verification levels, purchasers can precisely select and combine anti-counterfeiting technologies based on their specific application scenarios, risk levels, and desired ease of verification. For example, high-value financial instruments or identification documents might require a combination of all three levels for multi-layered protection, while everyday internal documents might focus on easily recognizable overt features. This tailored approach helps optimize resource allocation, avoid unnecessary costs, and ensure that the security of critical documents is adequately safeguarded.
Overt Features: The Cornerstone of Instant Verification
These features are visible to the naked eye and can be verified without special tools, serving as the first line of defense to provide quick and convenient authentication for general users.
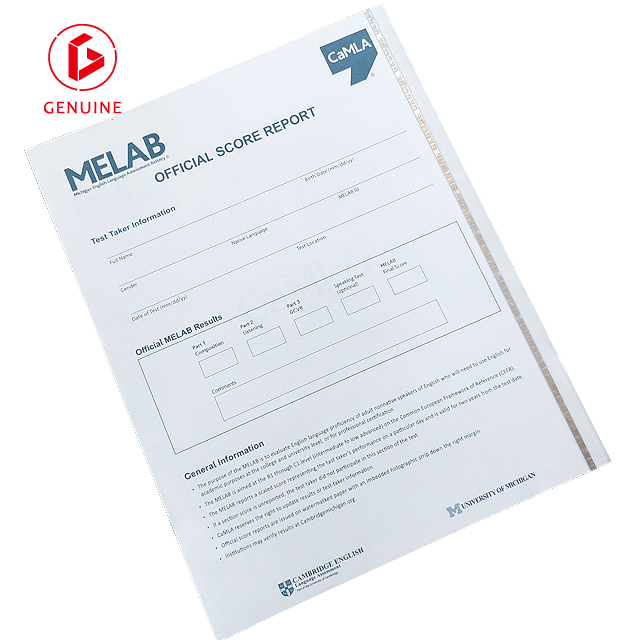
Watermark Paper: A watermark is a pattern or image formed during the papermaking process by varying the paper pulp density, visible when held to light. Because it is an integral part of the paper and formed during manufacturing, it is virtually impossible to counterfeit and cannot be transferred from other documents. We offer standard watermark designs, and we can also customize exclusive watermarks, such as your company logo or specific text, to meet your brand or specific needs. Production lead times and bulk requirements for custom watermarks (e.g., 2,000+ A4 for smaller quantities, 200,000+ A4 for larger orders) need to be planned in advance. The introduction of custom watermarks deeply integrates anti-counterfeiting functionality with brand identity. It is not just a security feature, but an extension of your brand image, capable of enhancing the overall perceived value and uniqueness of the document.

Security Thread Paper: A security thread is a metallized or polymer thread embedded within the paper, visible when held to light or partially exposed on the paper surface. These are extremely difficult to copy, especially when Optically Variable Ink (OVI) is used, which changes color depending on the viewing angle (e.g., from green to blue). However, it is important to note that some holographic threads might be mimicked with simple foil, requiring careful verification. This caution regarding potential counterfeiting methods demonstrates our deep understanding of the “arms race” in anti-counterfeiting. It’s not enough to simply have a security feature; it must be robust enough to withstand increasingly sophisticated replication attempts. This emphasizes the importance of continuous innovation and a multi-layered security strategy to ensure your anti-counterfeiting system always stays ahead of counterfeiters.
Void Pantographs: This is a clever design where a hidden message (e.g., “COPY ALERT”) is largely indistinguishable from the background on the original document, but becomes clearly visible when the document is photocopied or scanned. This provides immediate and obvious evidence of document copying.
Thermochromatic Ink: This special ink changes color with temperature variations, for instance, fading or changing color when rubbed or exposed to heat. This dynamic change offers users a simple and intuitive verification method, exposing any attempts to tamper with the document through heating or cooling.
Scratchable Surface: Similar to lottery tickets or phone cards, a layer that reveals hidden information when scratched. This is suitable for scenarios requiring information to be revealed progressively or for single-use verification.
3D Numismatic Carved Text: Complex lines are woven to create a sculpted image or word, visible to the naked eye but extremely difficult to precisely reproduce due to its intricate structure.
Guilloche Backgrounds: Intricate patterns composed of precise, complex geometric lines, visible to the naked eye, but which blur or disappear when copied, and completely vanish if text erasure is attempted.
Bleeding Ink: Simply rubbing a wet finger on the printed area will produce a bleeding effect, instantly authenticating the document. This effect cannot be photocopied or digitally recreated.
Penetrating Numbering: The colorant in this ink penetrates into the paper and appears as a mark (e.g., a pink marking) on the reverse side. This makes the numbering difficult to erase or tamper with.
Covert Features: Assurance Through Professional Verification
These features are invisible to the naked eye and require specific devices (such as UV light or a magnifying glass) for verification, providing a higher level of authentication for professionals.
- UV Fiber Paper: This security paper contains Ultraviolet (UV) fibers that are invisible to the naked eye but become visible and fluoresce under UV light. It is difficult for counterfeiters to precisely mimic the pattern and distribution of these UV fibers.
- Microprinting: This refers to extremely small text or patterns that are difficult to discern with the naked eye and typically require a magnifying glass to read. Due to their minuscule size, they blur or disappear when photocopied or scanned. The relatively low cost of microprinting makes it a cost-effective security option.
- Chemical Sensitized Paper/Ink: The paper or ink is sensitive to certain chemicals (such as bleach, solvents, acids/alkalines). When the document is tampered with, these areas will change color, smudge, or disappear, leaving clear evidence of alteration. For example, solvent-sensitive ink will smudge when attacked with solvents, showing instant visibility of the attack.
- Paper without Optical Brightening Agent (OBA-free): This type of paper, similar to that used for banknotes and checks, is inert to UV light, ensuring that invisible UV ink printed on it is clearly visible under UV light, thereby highlighting its anti-counterfeiting effect.
- Invisible UV Ink Image/Text: Images or text printed with invisible UV ink are not visible to the naked eye but become visible and fluoresce only under UV light, available in various colors (yellow, blue, red, green). This is an effective covert security feature, allowing only authorized personnel to verify the document as genuine.
- Chromotropic Ink: This ink is visible to the naked eye in one color (e.g., blue) but changes to another color (e.g., red) under UV light. This provides a dual layer of verification.
- Secure Front-to-Back Inking: This printing technique ensures that an image or shape is printed on both sides of the sheet, and when viewed through light, the patterns align perfectly to form a complete image. This is extremely difficult to counterfeit.
Forensic-Level Features: The Highest Tier of Security
These features require highly specialized tools and techniques for detection, used for the highest level of anti-counterfeiting to resist the most sophisticated forgery attempts.
- Taggants (Chemical “DNA”): Taggants are microscopic chemical markers added to the coating or paper pulp that can only be decoded by special means, providing a unique identifier. They act like the product’s “chemical DNA,” providing a unique authentication for the product.
- Soft Magnetic Microwire: These microwires are embedded within the security paper and can be detected by Electromagnetic Article Surveillance (EM EAS) systems or high-sensitivity metal detectors. This technology is primarily used to prevent unauthorized removal of documents such as trade secrets, blueprints, or government files.
- Encrypted Sequential Number: This type of serial number features a variable check key, making it impossible to predict the next number. It can be printed with penetrating, migrating, and chromotropic black ink, ensuring it cannot be erased and changes color under UV light, even migrating to the back of the paper, further enhancing its anti-counterfeiting capabilities.
Cost-Effectiveness Evaluation: Total Cost of Ownership (TCO) and Return on Investment (ROI)
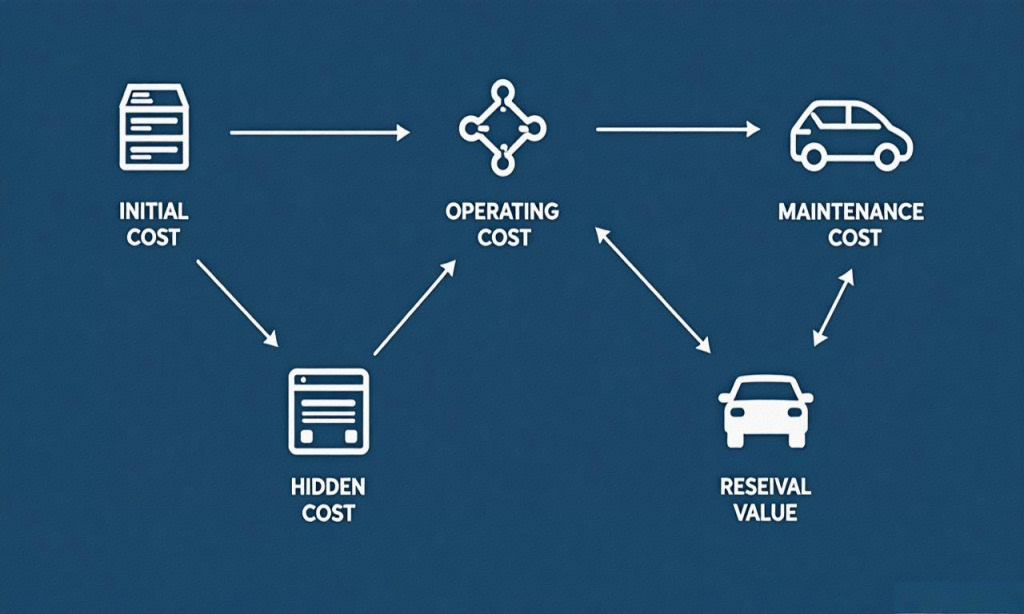
Understanding Total Cost of Ownership (TCO): Beyond the Purchase Price
Total Cost of Ownership (TCO) is a comprehensive methodology for quantifying all expenses associated with a product or service throughout its entire lifecycle. It goes beyond the initial purchase price and includes:
- Initial Cost: The upfront purchase price of the asset, which often represents only a fraction of its total cost over its lifespan.
- Operational Costs: Ongoing expenses related to document handling, storage, distribution, and routine verification.
- Maintenance Costs: Any necessary system maintenance or upgrade costs to ensure the effectiveness and readability of security features.
- Hidden Costs: This is a crucial yet often overlooked part of TCO analysis. It includes significant losses due to counterfeiting and fraud, such as revenue loss, market share erosion, legal fees, regulatory fines, brand damage, customer churn, product recalls, investigation costs, and supply chain disruptions.
- Residual Value: The value that may be recovered through resale or salvage at the end of the asset’s useful life, which is subtracted from the overall cost.
The TCO formula is: TCO = Initial Cost + Operational Costs + Maintenance Costs + Hidden Costs – Residual Value.
TCO analysis provides a holistic perspective, helping organizations make informed procurement decisions, optimize operations, and enhance cost efficiency. It emphasizes the importance of long-term benefits over short-term prices. For example, a case study in the manufacturing sector showed that while Equipment A had a lower initial cost, Equipment B offered a lower TCO due to its superior energy efficiency and lower maintenance requirements. This clearly illustrates that focusing solely on purchase price can lead to higher overall expenditures in subsequent operations. For bulk purchasers, by comprehensively calculating the TCO of security paper, they can clearly quantify potential losses due to counterfeiting and fraud, and integrate these into their decision-making. This demonstrates that a seemingly higher initial investment in robust security paper can lead to significant long-term savings by effectively mitigating these “hidden costs,” thereby justifying its financial prudence.
Measuring Return on Investment (ROI): The Value Proposition of Security Investment
Investment in anti-counterfeiting solutions should be evaluated through ROI to quantify its financial returns. ROI is not merely about offsetting costs; it’s about creating value.
The components of ROI include:
- Reduced Revenue Loss: Effective anti-counterfeiting measures can significantly reduce market share erosion and sales losses caused by counterfeit products. For example, the pharmaceutical industry restored 25% of lost revenue through product serialization and saved USD 1 million in legal fees. This directly translates to higher net profits.
- Reduced Brand Protection Costs: Robust anti-counterfeiting solutions can lower costs associated with legal disputes, product recalls, regulatory fines, and investigations caused by counterfeits. By proactive prevention, businesses can avoid expensive remediation costs.
- Enhanced Customer Trust and Loyalty: Increased consumer confidence in product authenticity leads to repeat purchases and higher customer lifetime value. For example, the luxury goods industry saw a 20% sales increase through QR code authentication because customers regained confidence in original products. This trust-building is an intangible asset crucial for long-term business growth.
- Increased Market Competitiveness: Brands that invest in anti-counterfeiting measures stand out in the industry, gaining a competitive advantage by offering a higher level of security and authenticity. In markets where counterfeiting is prevalent, this differentiation helps brands maintain pricing power and expand into new markets.
- Improved Operational Efficiency: Track-and-trace technologies (such as serialization and QR codes) streamline supply chain management, enabling early detection and removal of counterfeit products, thereby reducing costs associated with handling returns, customer complaints, and damaged goods. This not only saves resources but also optimizes resource allocation.
Research indicates that anti-counterfeiting efforts have a positive impact on the selling price of branded products and firm profits. This implies that security paper is not merely a cost-saving tool, but a strategy for generating revenue by enhancing brand value and consumer willingness to pay. When consumers perceive a higher level of authenticity and security, they are often willing to pay a premium, directly contributing to higher profit margins and overall revenue growth. Thus, investing in security transforms it from a defensive cost center into an active profit driver.
Strategic Benefits of Security Paper: Supply Chain Resilience and Compliance
Bolstering Supply Chain Resilience
Supply chain resilience refers to the ability of supply chains to quickly respond, adapt, and recover from disruptive events. Security paper enhances supply chain resilience in the following ways:
- Mitigating Counterfeit Infiltration: Counterfeit products disrupt supply chains, damage brand reputation, and pose safety risks. The anti-counterfeiting features provided by security paper effectively identify and prevent counterfeit products from entering the supply chain. This reduces potential supply chain contamination at its source.
- Improving Supply Chain Visibility and Traceability: Security paper with features like serialization, QR codes, or Taggants enables end-to-end tracking of products from production to distribution, allowing for timely detection of anomalies and counterfeiting activities. This enhanced visibility allows procurement and supply chain managers to identify irregularities (e.g., unexpected product quantities, unusual shipping routes) that might indicate counterfeiting or other disruptions. Early detection means faster intervention, thereby reducing the “Time to Recover” from a disruption and minimizing its impact. This proactive capability transforms security paper from a mere reactive anti-fraud tool into a fundamental component of a resilient supply chain strategy.
- Reducing Operational Disruption Risks: By ensuring the authenticity of documents and products, security paper helps avoid operational disruptions caused by fraud, product recalls, or regulatory interventions. Stable operations are at the core of supply chain resilience.
- Building Trust and Reliability: A secure supply chain is a reliable one, which translates into a competitive advantage as clients and partners trust organizations that prioritize end-to-end security. This trust relationship forms the cornerstone of long-term collaboration and market credibility.

Ensuring Regulatory Compliance
Procurement compliance means ensuring all purchasing activities adhere to applicable regulations, laws, internal policies, and external guidelines. Security paper plays a crucial role in the following aspects:
- Meeting Industry Standards and Legal Requirements: Many industries (e.g., finance, healthcare, government) have strict regulations regarding document authenticity and security. For example, the United States requires all birth certificates to be issued on “safety paper” to prevent tampering or counterfeiting. Organizations like ASTM International and TAPPI establish standards for the paper and printing industries, ensuring products meet stringent quality and security specifications.
- Preventing Fraud and Corruption: Compliant procurement processes minimize opportunities for fraudulent activities (e.g., bribery, kickbacks). Security paper, as a physical line of defense, directly reduces the risk of document fraud, such as forged certificates or tickets.
- Protecting Sensitive Information: Through built-in anti-counterfeiting features, security paper ensures that documents containing Personally Identifiable Information (PII), financial data, or trade secrets are not unauthorizedly copied, altered, or disclosed. This is critical for complying with data privacy regulations (e.g., GDPR).
- Enhancing Audit Readiness: Documents with verifiable security features provide a clear audit trail, demonstrating that procurement and document management comply with regulations. This not only simplifies audit processes but also enhances transparency. Beyond legal mandates, robust document security (enabled by security paper) significantly enhances audit readiness and protects against reputational damage. This transforms compliance from a burden into a competitive advantage and a trust-building mechanism. When documents feature verifiable anti-counterfeiting elements, businesses can more easily demonstrate to auditors, regulators, and partners the rigor of their procurement and document management processes. This transparency and traceability not only reduce the risk of fines and legal repercussions due to non-compliance but, more importantly, build the company’s credibility in the market, strengthening its image as a responsible and trustworthy partner.
Challenges and Solutions in Bulk Procurement
Challenges in International Procurement
International procurement, especially involving high-value or sensitive documents, faces numerous challenges, with document fraud being particularly prominent:
- Document Fraud: Falsifying or manipulating trade documents such as bills of lading, invoices, or certificates of origin is a common fraudulent practice in international trade. This can lead to misdirected shipments, incorrect payments, or even illegal transactions.
- Supply Chain Complexity: International trade involves multiple parties, jurisdictions, and complex regulatory frameworks, making it extremely difficult to maintain transparency and verify the authenticity of all aspects of a transaction. This complexity creates opportunities for fraudsters.
- Vulnerability of Paper-Based Processes: Traditional paper documents are susceptible to forgery, alteration, and easy replication, posing significant challenges to detecting fraudulent activities.
- Lack of End-to-End Visibility: In global supply chains, a lack of end-to-end visibility into the movement of goods and the legitimacy of transactions makes it difficult for financial institutions to verify transaction authenticity. This opacity can be exploited by fraudsters to misrepresent the status or value of shipments.
- Evolving Fraud Techniques: Fraudsters continuously update their methods, leveraging advanced technologies for counterfeiting, putting immense pressure on traditional anti-counterfeiting measures.
Solutions: Strategic Procurement and Customized Security Paper
To address these challenges, bulk purchasers need to adopt strategic procurement approaches and integrate customized security paper as a core solution:
- Vendor Consolidation and Long-Term Partnerships: Establishing long-term relationships with a few reliable and reputable security paper suppliers can secure volume discounts and more favorable contract terms. This not only simplifies the procurement process but also ensures supply chain stability and consistent product quality.
- Customized Security Paper Solutions: Tailoring security features to specific application scenarios (such as passports, certificates, banknotes, legal documents) ensures the highest level of protection. For example, passports can embed electronic chips and custom watermarks , while certificates can utilize multi-tone watermarks and embedded fibers. This customization allows for precise alignment with your risk requirements, providing the most cost-effective anti-counterfeiting solution.
- Technology Integration and Automation: Combining digital platforms, Artificial Intelligence (AI), machine learning, and blockchain technologies enhances document verification, tracking, and risk assessment capabilities. For instance, blockchain technology can create immutable transaction records, significantly reducing the risk of document fraud. Digital document management systems also significantly improve efficiency and reduce costs.
- Regular Audits and Employee Training: Conducting regular procurement audits to identify and address compliance gaps is crucial. Simultaneously, providing employees with training on anti-counterfeiting identification and compliance is essential to ensure they are aware of the latest anti-counterfeiting technologies and verification processes.
Conclusion and Outlook
Security paper technology plays an indispensable role in combating the escalating global threats of counterfeiting and fraud. For you, as a bulk purchaser, investing in security paper is no longer just an item on a procurement list; it is a strategic initiative with profound implications. It effectively lowers your Total Cost of Ownership (TCO) by reducing revenue losses, legal fees, and brand damage caused by fraud, thereby delivering a substantial Return on Investment (ROI).
More importantly, security paper is a critical cornerstone for building a resilient supply chain and ensuring regulatory compliance. It enhances document authenticity, traceability, and tamper-resistance, thereby bolstering your ability to withstand supply chain disruptions and ensuring your operations adhere to increasingly stringent international standards and legal regulations. In today’s era of digital transformation and increasingly complex global trade, the integration of security paper’s physical anti-counterfeiting features with digital verification technologies provides your enterprise with multi-layered, comprehensive protection.
We at Genuine Printing are committed to being your trusted partner, providing you with the most cutting-edge and reliable security paper solutions. We encourage you to re-evaluate your current document security strategy and consult with our expert team to jointly build a more secure and resilient future for your business.
Is your procurement strategy prepared for the increasingly complex security challenges of tomorrow?